Formamos recursos humanos de pregrado, grado y postgrado, promovemos la investigación científica y tecnológica, capacitamos en forma permanente, nos vinculamos, transferimos y brindamos servicios de calidad a la sociedad.
miércoles, 29 de abril de 2020
domingo, 26 de abril de 2020
How To Secure Your Home Against "Internet Of Things" And FUD
TL;DR, most of the security news about IoT is full of FUD. Always put the risks in context - who can exploit this and what can the attacker do with it. Most story only covers the latter.
Introduction
There is rarely a day without news that another "Internet of Things" got hacked. "Smart" safes, "smart" rifles, "smart" cars, "smart" fridges, "smart" TVs, "smart" alarm systems, "smart" meters, "smart" bulbs, NAS devices, routers. These devices are getting hacked every day. Because most of these devices were never designed with security as a goal, and some of them have been never tested by security professionals, it is no surprise that these things are full of vulnerabilities.
Independent security researchers find these vulnerabilities, write a cool blog post or give a presentation about the vulnerability and the exploit, and the media forgets the constraints just for the sake of more clicks. "We are all doomed" we can read in the news, but sometimes the risks are buried deeply in technical jargon. Please note I blame the news sites here, not the researchers.
 |
| http://www.slideshare.net/danielmiessler/iot-attack-surfaces-defcon-2015 |
There are huge differences between the following risks:
- Attackers can directly communicate with the router (or camera) from the Internet without authentication and exploit the vulnerability. This is the worst-case scenario. For example, an automated ransomware attack against your NAS is pretty bad.
- Attackers have to position themselves in the same WAN network (e.g. Sprint mobile network in the case of Jeep hacking) to exploit the vulnerability. This is still pretty bad.
- The vulnerable code can not be triggered directly from the Internet, but tricks like CSRF can be used to exploit it (details later in this post).
- The vulnerable code can not be triggered directly from the Internet, and it uses a protocol/port which prevents Cross Protocol Scripting. Attackers have to access the local network before exploiting this vulnerability.
As it is the case with the worst scenario, one can find a lot of devices connected to the internet. You can always find funny stuff at http://explorer.shodanhq.com/#/explore , or use the nmap screenshot script to find your own stuff :)
Network exposure
Most devices are behind an IPv4 NAT device (e.g. home router), thus can not be reached from the Internet side by default. Except when the device configures the firewall via UPNP. Or the device has a persistence cloud connection, and the cloud can send commands to the device. Or the device uses IPv6 tunneling (e.g. Teredo), thus it is reachable from the Internet. But not every vulnerability on your home network is accessible directly from the Internet. As more and more devices and networks will support IPv6, this scenario might change, but I hope most home routers will come with a default deny configuration in their IPv6 firewall module. On the other hand, scanning for IPv6 devices blindly is not feasible due to the large number of IPv6 addresses, but some tricks might work.
If attackers can not access the device directly, there is a way to hack it through the user's browser. Just convince the victim user to visit a website, and via CSRF (Cross Site Request Forgery) and brute-forcing the device IP, it is possible to hack some devices (mostly through HTTP - if the exploit can fit into simple GET or POST commands.
If attackers can not attack the device vulnerability through the Internet directly, or via CSRF, but have connected to the same network - the network exposure shrinks significantly. And when attackers are on the same network as you, I bet you have bigger problems than the security of the IoT devices ...
Recommendations for home users
Don't buy **** you don't need
Disconnect from the power cord the IoT devices you don't need to operate 7*24.
Disconnect from the power cord the IoT devices you don't need to operate 7*24.
Disable cloud connectivity if it is not necessary. For example, I have a NAS device that can be reached through the "cloud", but I have disabled it by not configuring any default gateway for the device. I prefer connecting to my network via VPN and reach all my stuff through that.
Prevent CSRF attacks. I use two tricks. Don't use the 192.168.0.x - 192.168.10.x network at-home - use an uncommon IP range instead (e.g. 192.168.156.x is better). The second trick is I configured my Adblock plugin in my primary browser to block access to my internal network. And I use another browser whenever I want to access my internal devices. Update: On Firefox you can use NoScript ABE to block access to internal resources.
Check your router configuration:
- disable UPnP
- check the firewall settings and disable unnecessary port forwards
- check for IPv6 settings, and configure the firewall as default deny for incoming IPv6 TCP/UDP.
Change default passwords, especially for services connected to the Internet. Follow password best practices.
Run Nmap to locate new IoT in your home network :)
Run a WiFi scan to locate new WiFi access points. Let me share a personal experience with you. I moved to a new house and brought my own WiFi router with me. I plugged it in, and forget about WiFi. Months later it turned out I had two other WiFi devices in my house - the cable modem had its own integrated WiFi with default passwords printed on the bottom, and the Set-top-box was the same - default WiFi passwords printed on the bottom. And don't forget to scan for ZigBee, Bluetooth, IrDA, FM, ...
Update your devices - in case you have a lot of free time in your hand.
Don't allow your guests to connect to your home network. Set up a separated AP for them. Imagine your nephew stealing your private photos or videos from your NAS or DNLA server.
With great power, comes great responsibility. The less device you own in your house, the less time you need to maintain those.
Read the manuals of your devices. Be aware of the different interfaces. Configure it in a secure way.
Disable Teredo protocol in case you don't need IPv6.
Stop being amazed by junk hacking.
Update: Disable WebRTC: https://www.browserleaks.com/webrtc , in Chrome you can use this extension: https://chrome.google.com/webstore/detail/webrtc-network-limiter/npeicpdbkakmehahjeeohfdhnlpdklia
Update: Disable WebRTC: https://www.browserleaks.com/webrtc , in Chrome you can use this extension: https://chrome.google.com/webstore/detail/webrtc-network-limiter/npeicpdbkakmehahjeeohfdhnlpdklia
Update: Prevent against DNS rebind attacks via configuring a DNS server which can block internal IP addresses. OpenDNS can block internal IP, but this is not a default option, you have to configure it.
Recommendations for vendors
For vendors, I recommend at least the followings:
- Implement security during Software Development LifeCycle
- Continuous security testing and bug bounties
- Seamless auto-update
- Opt-in cloud connectivity
Recommendations for journalists
Stop FUD. Pretty please.
The questions to ask before losing your head
- who can exploit the vulnerability?
- what prerequisites do we have about the attack to successfully exploit the vulnerability? Is the attacker already in your home network? If yes, you have probably bigger problems.
- what can the attacker do when the exploit is successful?
And last but not least, don't forget that in the case of IoT devices, sometimes users are the product, not the customer. IoT is about collecting data for marketing purposes.
Vsftpd Backdoor - Ekoparty Prectf - Amn3S1A Team
It's a 32bits elf binary of some version of vsftpd, where it have been added a backdoor, they don't specify is an authentication backdoor, a special command or other stuff.
I started looking for something weird on the authentication routines, but I didn't found anything significant in a brief period of time, so I decided to do a bindiff, that was the key for locating the backdoor quickly. I do a quick diff of the strings with the command "strings bin | sort -u" and "vimdiff" and noticed that the backdoored binary has the symbol "execl" which is weird because is a call for executing elfs, don't needed for a ftp service, and weird that the compiled binary doesn't has that symbol.
Looking the xrefs of "execl" on IDA I found that code that is a clear backdoor, it create a socket, bind a port and duplicate the stdin, stdout and stderr to the socket and use the execl:
There are one xrefs to this function, the function that decides when trigger that is that kind of systems equations decision:
The backdoor was not on the authentication, it was a special command to trigger the backdoor, which is obfuscated on that systems equation, it was no needed to use a z3 equation solver because is a simple one and I did it by hand.
The equation:
cmd[0] = 69
cmd[1] = 78
cmd[1] + cmd[2] = 154
cmd[2] + cmd[3] = 202
cmd[3] + cmd[4] = 241
cmd[4] + cmd[5] = 233
cmd[5] + cmd[6] = 217
cmd[6] + cmd[7] = 218
cmd[7] + cmd[8] = 228
cmd[8] + cmd[9] = 212
cmd[9] + cmd[10] = 195
cmd[10] + cmd[11] = 195
cmd[11] + cmd[12] = 201
cmd[12] + cmd[13] = 207
cmd[13] + cmd[14] = 203
cmd[14] + cmd[15] = 215
cmd[15] + cmd[16] = 235
cmd[16] + cmd[17] = 242
The solution:
cmd[0] = 69
cmd[1] = 75
cmd[2] = 79
cmd[3] = 123
cmd[4] = 118
cmd[5] = 115
cmd[6] = 102
cmd[7] = 116
cmd[8] = 112
cmd[9] = 100
cmd[10] = 95
cmd[11] = 100
cmd[12] = 101
cmd[13] = 106
cmd[14] = 97
cmd[15] = 118
cmd[16] = 117
cmd[17] = 125
The flag:
EKO{vsftpd_dejavu}
The binary:
https://ctf.ekoparty.org/static/pre-ekoparty/backdoor
The binary:
https://ctf.ekoparty.org/static/pre-ekoparty/backdoor
15 Important Run Commands Every Windows User Should Know
There are several ways to efficiently access the files, folders, and programs in Windows operating system. We can create shortcuts, pin programs to the taskbar, Start menu shortcuts etc. but we can't do it for all programs in many cases. However, the Windows Run Command box is one of the most efficient ways of accessing system programs, folders, and settings.
In this article, I am going to share 15 most important Run commands for Windows users. These commands can make it easier to manage a lot of tasks.
How to open Windows Run command box?
You need to press Win+R (Hold Windows button then Press R)
Important Run Commands Every Windows User Should Know
1. %temp%
This is the fastest way to clear the temporary files from your computer. It can save a lot of space which was being wasted by temporary files.
2. cmd
This command will open the windows DOS command prompt. Windows command prompt is very useful for performing many tasks which are not possible using graphical user interface.
3. MSConfig
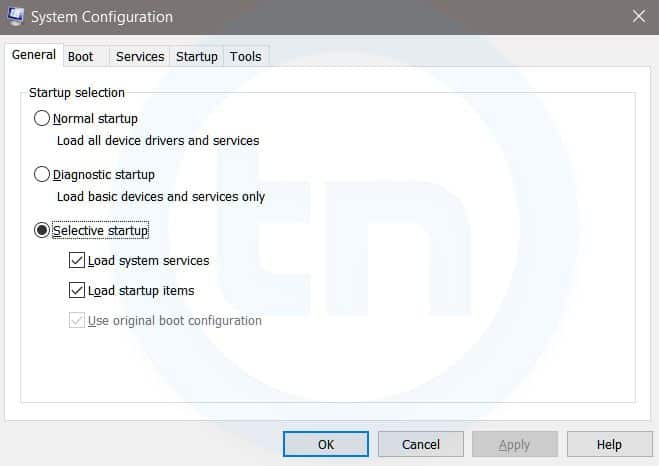
Windows System Configuration
This command will open Windows System Configuration where you can edit different things like the boot options, startup options, services, etc.
4. sysdm.cpl
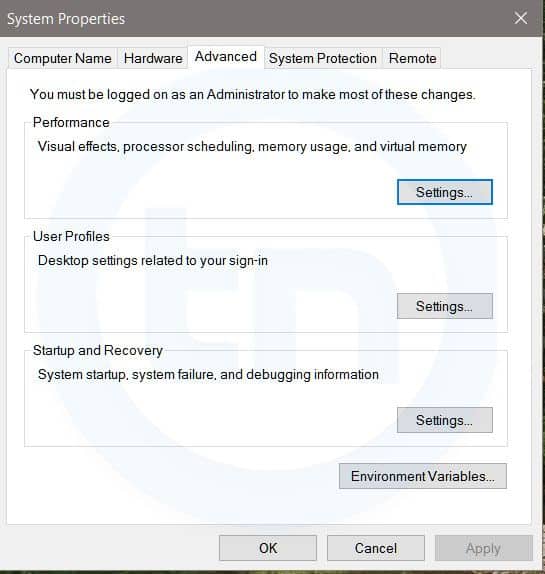
System Properties window
This command will open the System Properties window, Where you can change the system protection and performance related many settings
5. Powershell
Powershell is very similar the command prompt. Just type this command in the Run dialog box, and you will have your PowerShell opened without administrator privileges.
6. perfmon.msc
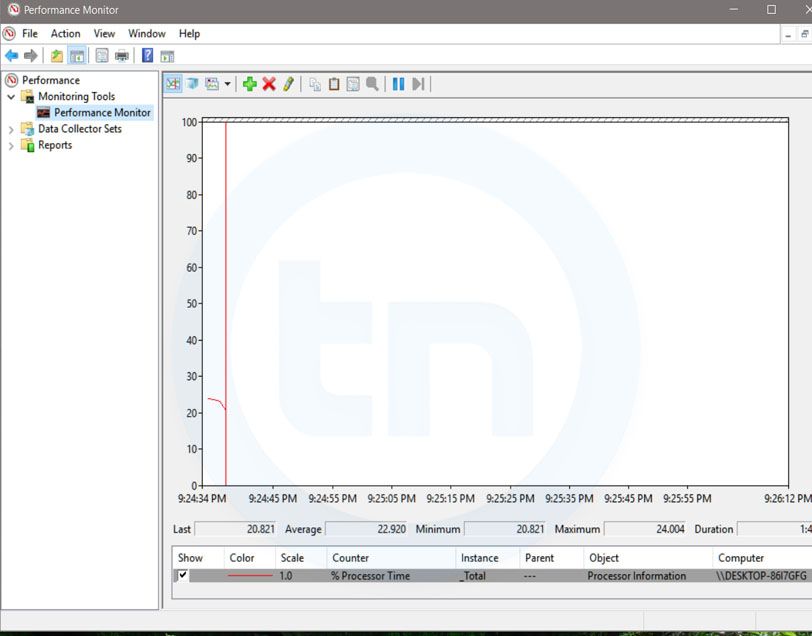
Windows System Performance monitor
This command can be used to monitor the performance of your computer. There are plenty of options for monitoring the system performance
7. regedit
Regedit Run command is used to open the Windows Registry. It is a hierarchical database that hosts all the configurations and settings of Windows operating system, it's users and the installed software.
8. \ (Backslash)
This is one of the lesser known Run commands. Just enter the backslash into the Run dialog box and it will open up the C drive. It is one of the quickest ways to access the C drive.
9. . (Dot)
This is yet another lesser known Run command. When executed, it opens the current user's home folder which hosts all the other local folders like the Downloads, Documents, Desktop, Pictures, etc.
10. .. (Double Dots)
When you execute these two dots in the Run dialog box, it will open up the Users folder which is located directly on the C drive
Also Read; Top 10 Great Gifts For Hackers
11. Control
This command will open the control panel. Control panel is used for managing all the system settings and programs
12. hdwwiz.cpl
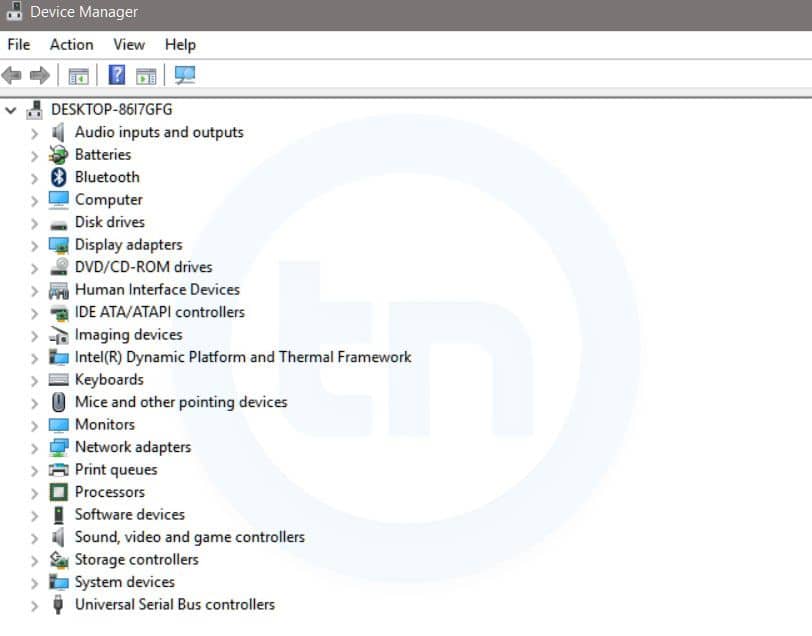
Windows Device Manager
This command is used to open the Device Manager in Windows. You can manage all the device connected internally or externally to your PC.
13. Notepad
The quickest way to open notepad in Windows. Just type this command in Run Box and hit enter.
14. osk
This command will open On-Screen Keyboard on your display monitor. You can easily touch and type or use your mouse for typing.
15. taskmgr
This command will open task manager where you can manage all the processes and programs running on Windows Operating system.
sábado, 25 de abril de 2020
Spaghetti: A Website Applications Security Scanner
About Spaghetti
Author: m4ll0k Spaghetti is an Open Source web application scanner, it is designed to find various default and insecure files, configurations, and misconfigurations. Spaghetti is built on Python 2.7 and can run on any platform which has a Python environment.
Spaghetti Installation:
Spaghetti's Features:
Fingerprints:
- Server:
- Web Frameworks (CakePHP,CherryPy,...)
- Web Application Firewall (Waf)
- Content Management System (CMS)
- Operating System (Linux,Unix,..)
- Language (PHP,Ruby,...)
- Cookie Security
- Bruteforce:Admin Interface
Common Backdoors
Common Backup Directory
Common Backup File
Common Directory
Common FileLog File - Disclosure: Emails, Private IP, Credit Cards
- HTML Injection
- SQL Injection
- LDAP Injection
- XPath Injection
- Cross Site Scripting (XSS)
- Remote File Inclusion (RFI)
- PHP Code Injection
- HTTP Allow Methods
- HTML Object
- Multiple Index
- Robots Paths
- Web Dav
- Cross Site Tracing (XST)
- PHPINFO
- .Listing
- ShellShock
- Anonymous Cipher (CVE-2007-1858)
- Crime (SPDY) (CVE-2012-4929)
- Struts-Shock
python spaghetti --url example.com --scan 0 --random-agent --verboseMore information
CEH: Gathering Network And Host Information, Types Of Scan
In Hacking the main focus is over gathering the information about victim or victim's machine. Which will help to find out which type of exploit will works according to the given circumstances. Gathering the network and host information means to find out by which network, the which victim's machine is connected and communicating over the network. Moreover, scanning is also performed for gathering information about open and closed ports. After that they'll able to find the vulnerabilities in the target system and try to get access to the system.
Types Of Scan
As a CEH you should know the scan types and uses:SYN
SYN scan doesn't complete the TCP three way handshake that is why it is known as a half-open scan. An attacker send a SYN packet to the victim machine if SYN/ACK packet is received back to attacker, then it clarify that the port is listening due to the acknowledgment by the victim that it has completed the connection. While if the attacker is received the RST/ACK packet then it assumed that the port is closed or open.XMAS
XMAS scan works only on target system that has the RFC 793 development of TCP/IP and it doesn't works against any version of windows.XMAS scan send a packet with by setting up the FIN, URG and PSH flags of the TCP header. The function of this scan is if the port is active there will be no response but if the port is closed the target responds with a RST/ACK packet.
FIN
A FIN scan send a packet by setting up only the FIN flag of the TCP. This scan is similar to XMAS scan. FIN scan receives no response if the port is active while if the port is closed it receives the RST/ACK packet.NULL
NULL scan is also similar to the XMAS scan. But the only difference is that it sends a packet without setting up the any flag of TCP header. NULL scan receives no response if the port is open but if the port is closed it receives the RST/ACK packet.IDLE
It is just like spoofing an IP address by sending a SYN packet to the victim's machine to find out which services are available over the system. This scan is completed with the help of another system called as "Zombie" (that is not receiving or transmitting any information).More info
Vsftpd Backdoor - Ekoparty Prectf - Amn3S1A Team
It's a 32bits elf binary of some version of vsftpd, where it have been added a backdoor, they don't specify is an authentication backdoor, a special command or other stuff.
I started looking for something weird on the authentication routines, but I didn't found anything significant in a brief period of time, so I decided to do a bindiff, that was the key for locating the backdoor quickly. I do a quick diff of the strings with the command "strings bin | sort -u" and "vimdiff" and noticed that the backdoored binary has the symbol "execl" which is weird because is a call for executing elfs, don't needed for a ftp service, and weird that the compiled binary doesn't has that symbol.
Looking the xrefs of "execl" on IDA I found that code that is a clear backdoor, it create a socket, bind a port and duplicate the stdin, stdout and stderr to the socket and use the execl:
There are one xrefs to this function, the function that decides when trigger that is that kind of systems equations decision:
The backdoor was not on the authentication, it was a special command to trigger the backdoor, which is obfuscated on that systems equation, it was no needed to use a z3 equation solver because is a simple one and I did it by hand.
The equation:
cmd[0] = 69
cmd[1] = 78
cmd[1] + cmd[2] = 154
cmd[2] + cmd[3] = 202
cmd[3] + cmd[4] = 241
cmd[4] + cmd[5] = 233
cmd[5] + cmd[6] = 217
cmd[6] + cmd[7] = 218
cmd[7] + cmd[8] = 228
cmd[8] + cmd[9] = 212
cmd[9] + cmd[10] = 195
cmd[10] + cmd[11] = 195
cmd[11] + cmd[12] = 201
cmd[12] + cmd[13] = 207
cmd[13] + cmd[14] = 203
cmd[14] + cmd[15] = 215
cmd[15] + cmd[16] = 235
cmd[16] + cmd[17] = 242
The solution:
cmd[0] = 69
cmd[1] = 75
cmd[2] = 79
cmd[3] = 123
cmd[4] = 118
cmd[5] = 115
cmd[6] = 102
cmd[7] = 116
cmd[8] = 112
cmd[9] = 100
cmd[10] = 95
cmd[11] = 100
cmd[12] = 101
cmd[13] = 106
cmd[14] = 97
cmd[15] = 118
cmd[16] = 117
cmd[17] = 125
The flag:
EKO{vsftpd_dejavu}
The binary:
https://ctf.ekoparty.org/static/pre-ekoparty/backdoor
The binary:
https://ctf.ekoparty.org/static/pre-ekoparty/backdoor
More information
jueves, 23 de abril de 2020
Networking | Switching And Routing | Tutorial 3 | 2018
Welcome to my 3rd new tutorial of networking (Routing and Switching). In this blog you will able to watch an interesting video about basic device navigation such as changing device (router or switch) name, configuration of login password, configuring a device information, router IP addresses and many more.
What is router?
Router is a network layer device which is the 3rd layer in the OSI model which is used to communicate different networks. It is an intelligent device fixed at the boundary of network that connects to other networks and responsible for end to end delivery of the packet that requires an IP address which is known as the logical address which is the basic identity of the device just like our identity card number or roll number and so on, for the identification of source and destination devices. Router is the gateway of the network having two interfaces such as inbound and the outbound interface through which the traffic comes in from different networks and comes out traffic to the different networks.What is an IP address?
Internet protocol (IP) address is a numeric label given to each and every device in the network for the identification of the device just like our roll numbers in collages, universities which identity each and every student uniquely everywhere. So same concept here, it is a logical address which is used whenever the device want to communicate outside the network that means to another network.What is Switch?
Switch is basically layer 2 device, which is used to connect two or more than two devices with each other in the same network. It is an intelligent device which doesn't allow the broadcast. It requires Media access control (MAC) address to communicate within the network. Now let's move to the video for further.More information
miércoles, 22 de abril de 2020
Files Download Information
After 7 years of Contagio existence, Google Safe Browsing services notified Mediafire (hoster of Contagio and Contagiominidump files) that "harmful" content is hosted on my Mediafire account.
It is harmful only if you harm your own pc and but not suitable for distribution or infecting unsuspecting users but I have not been able to resolve this with Google and Mediafire.
Mediafire suspended public access to Contagio account.
The file hosting will be moved.
If you need any files now, email me the posted Mediafire links (address in profile) and I will pull out the files and share via other methods.
P.S. I have not been able to resolve "yet" because it just happened today, not because they refuse to help. I don't want to affect Mediafire safety reputation and most likely will have to move out this time.
The main challenge is not to find hosting, it is not difficult and I can pay for it, but the effort move all files and fix the existing links on the Blogpost, and there are many. I planned to move out long time ago but did not have time for it. If anyone can suggest how to change all Blogspot links in bulk, I will be happy.
P.P.S. Feb. 24 - The files will be moved to a Dropbox Business account and shared from there (Dropbox team confirmed they can host it )
The transition will take some time, so email me links to what you need.
Thank you all
M
More info
Top 5 Most Useful Linux Tools For Programmers
Linux is a free and open-source software operating systems built around the Linux kernel. It typically packaged in a form known as a Linux distribution for both desktop and server use. It is a great development environment for programmers and developers. However, without the development tools, that would be impossible. Fortunately, plenty of Linux tools are available. Here are the top 5 most useful Linux tools for programmers.
Also Read;- How To Clone One Android To Another
5 Most Useful Linux tools for Programmers
1. VIM

VIM is a free and open source software written by Bram Moolenaar in 1991. It is designed for use both from a command-line interface and as a standalone application in a graphical user interface. It comes standard with almost every Linux distribution and is also known as "the programmer's editor". VIM is great for coding and can also be used for editing things like configuration files and XML documents.
Vim has been developed to be a cross-platform that supports many other platforms. In 2006, it was voted as the most popular editor amongst Linux Journal readers. In 2015, Stack Overflow developer survey found it to be the third most popular text editor while in 2016, the Stack Overflow developer survey found it to be the fourth most popular development environment.
Read more;- How To Use WhatsApp without Mobile No2. Zsh
Zsh is written in C and initially released in 1990. It is a Unix shell that can be used as an interactive login shell and as a powerful command interpreter for shell scripting. Zsh is an extended version of Bourne shell (BASH) with a large number of improvements, including some features of Bash, ksh, and tcsh. Zsh gives a user-friendly experience on the command line. It also gives better auto-completion, Vim key bindings, and smart guesses when you write a command wrong.
Its features include (but not limited to):
- Programmable command-line completion,
- Sharing of command history among all running shells
- Extended file globbing
- Improved variable/array handling
- Editing of multi-line commands in a single buffer
- Spelling correction
- Various compatibility modes,
- Themeable prompts, and
- Loadable modules.
3. Byobu
It was initially released in 2009 written in Sh and Python. Byobu can be used to provide on-screen notification or status and tabbed multi-window management. Thus, it is intended to improve terminal sessions when users connect to remote servers with an operating system Linux and Unix-like. It is is an enhancement for the GNU Screen terminal multiplexer or tmux used with the GNU/Linux computer operating system.
4. GIT
 Git was initially released on April 7, 2005. It is a version control system to track changes in computer files and to coordinate work on those files among multiple people. It is primarily used for source code management in software development and can be used to keep track of changes in any set of files available in the English language. It is aimed at speed, data integrity, and support for distributed, non-linear workflows. It is free and open source software distributed under the terms of the GNU General Public License version 2.
Git was initially released on April 7, 2005. It is a version control system to track changes in computer files and to coordinate work on those files among multiple people. It is primarily used for source code management in software development and can be used to keep track of changes in any set of files available in the English language. It is aimed at speed, data integrity, and support for distributed, non-linear workflows. It is free and open source software distributed under the terms of the GNU General Public License version 2.Moreover, Linus Torvalds was the creator of GIT for the development of the Linux kernel. On the other hand, its current maintainer since then is Junio Hamano. Thus, every Git directory on every computer is a full-fledged repository with complete history and full version tracking abilities, independent of network access or a central server.
Read more;- How To change Facebook Default Theme
5. Docker
Written by Solomon Hykes in 2013, it is a computer program that performs operating-system-level virtualization, the containerization, which is developed by Docker, Inc. Primarily, Docker was developed for Linux to use as the resource isolation features of the Linux kernel. It is a tool that can package an application and its dependencies in a virtual container that can run on any Linux server. This helps enable the flexibility and portability on where the application can run, whether on premises, public cloud, private cloud, bare metal, etc. Moreover, it accesses the Linux kernel's virtualization features either directly using the libcontainer library.
Related articles
Suscribirse a:
Comentarios (Atom)



















